In this information age as we know it, museum robberies and bank heists are passé as crime has gone digital. With businesses holding a plethora of assets electronically, they stand to lose as much if not more in an information security breach as to its physical counterpart. The abundant data that we hold is not only intellectual property and critical to the business but is also used today in processes like data analytics to help gain competitive advantage over rivals. Hence, security for one’s computer systems and networks is without doubt, paramount. With Viruses, Malwares and Hackers at large, threats of cyber-attacks are ever increasing and its nature, getting more complex. We help you build a comprehensive IS strategy through the design of an IS architecture and the implementation of an IS Management System.
Highlights of the services we provide are:
- 1Evaluating the Risk of Exposure to Sensitive Customer Information and Business Critical Data and protecting it.
- 2Deliver Security Awareness and Training Programs for the betterment of our Customers.
- 3Formulate of Information Security Policies, Procedures and Standards through the implementation of an ISMS based on ISO27001 Guidelines
- 4Improve Physical Security through Access Management, Surveillance, Environment Monitoring and Safeguard Systems.
- 5Build an Identity and Access Management Systems by the implementation of appropriate physical and logical controls.
- 6Anti Virus, Phishing and Malware Analysis and Protection Services
- 7Design a Security Architecture that fortifies the Organisation's Infrastructure
- 8Perform Desktop, Server, Network and Wireless Systems Hardening and Web Applications and Database Security Testing and Defence
- 9Threats and Vulnerability Assessment along with Penetration Testing and Security Log Analysis and Management
- 10Regulatory Compliance for UKDPA, SAS70, PCI DSS, HIPAA in Information Security among others
IT Governance

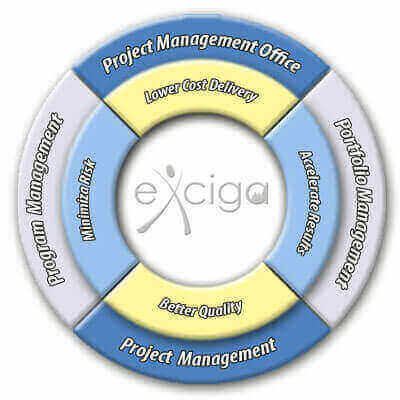
Project Mgmt
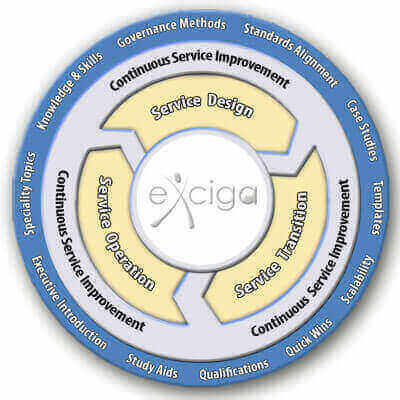
IT Service Mgmt
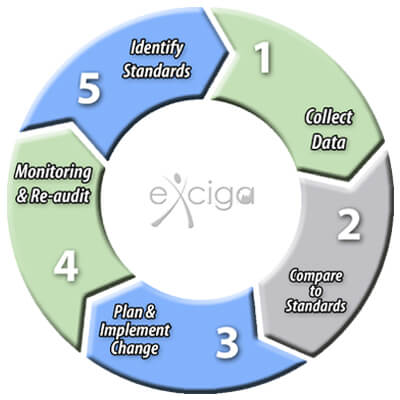
IS Audit
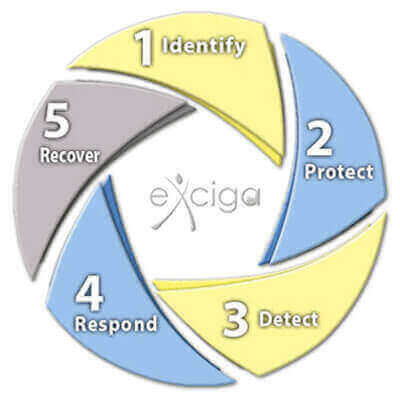
IS Security
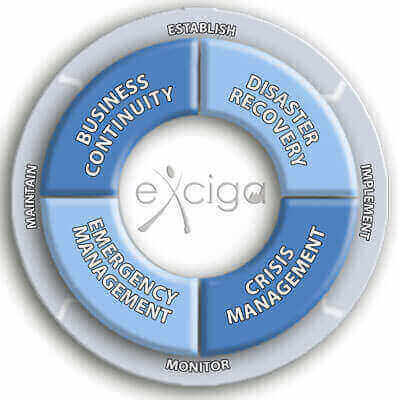
Business Continuity
Agile & Dev Ops

Product Mgmt









